troubleshoot-network-issues-using-ifconfig-command-in-linux
ifconfig-command
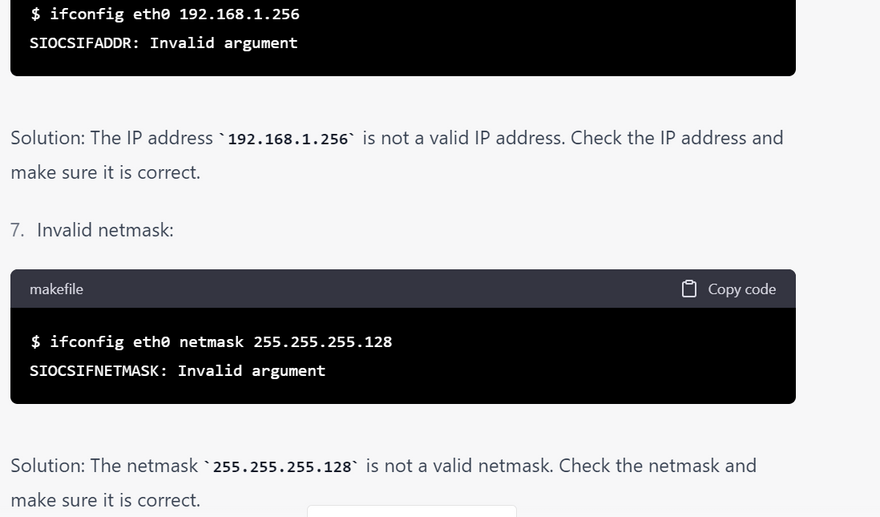
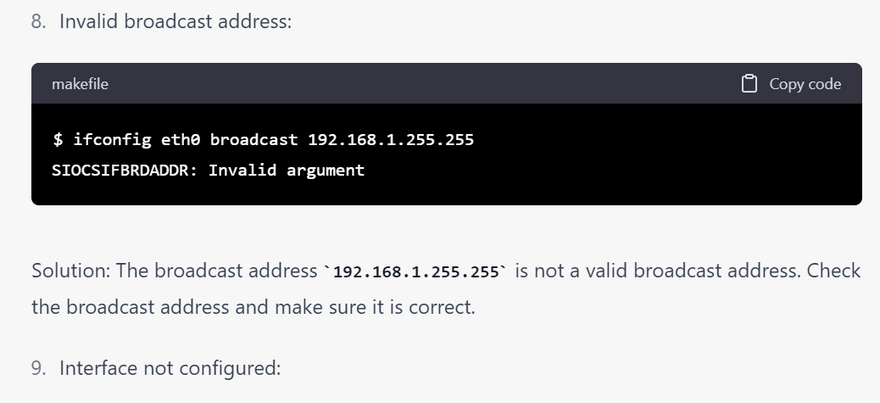
checklist of error for ifconfig commands with examples
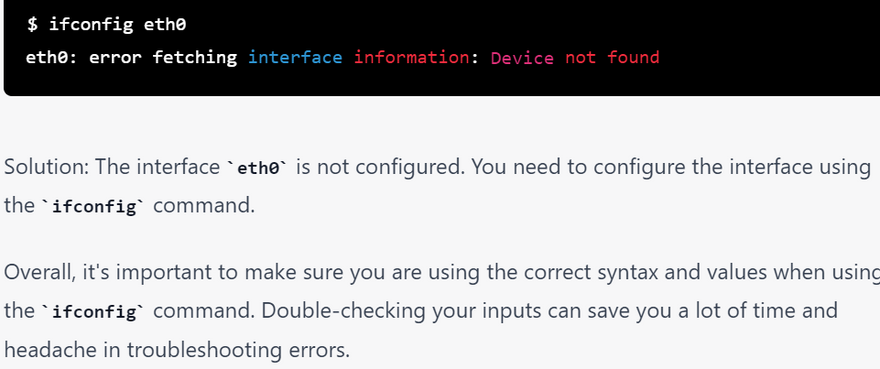
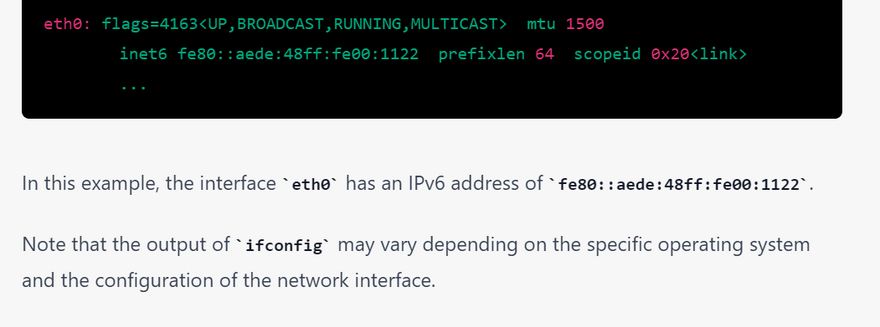
what do you mean by inet ,netmask,boardast,inet6 in ifconfig with examples
why broadcast address is used with example
why netmask is used with example
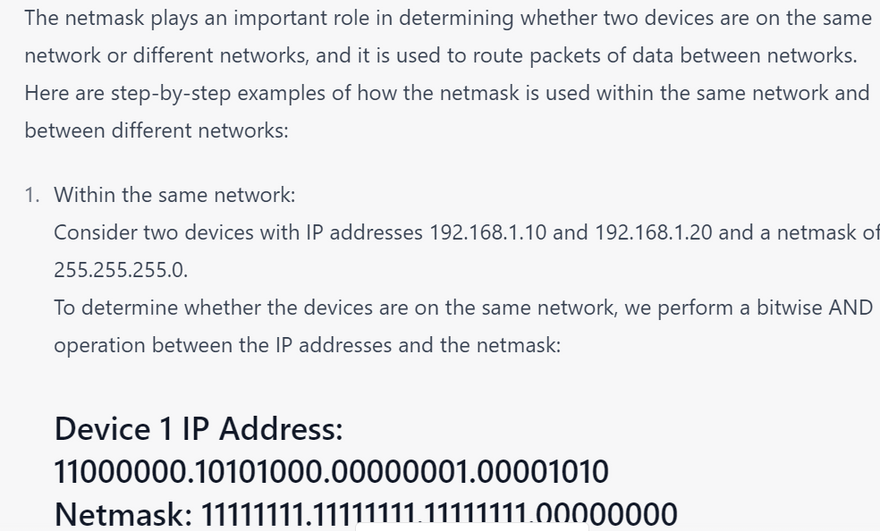
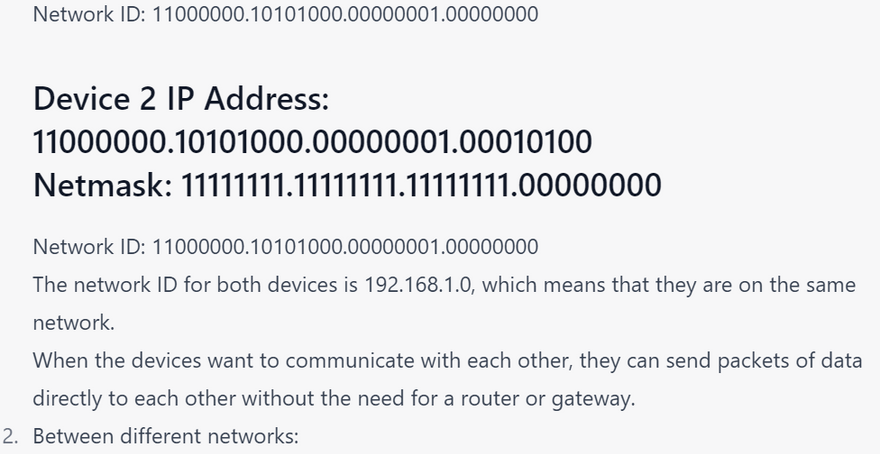
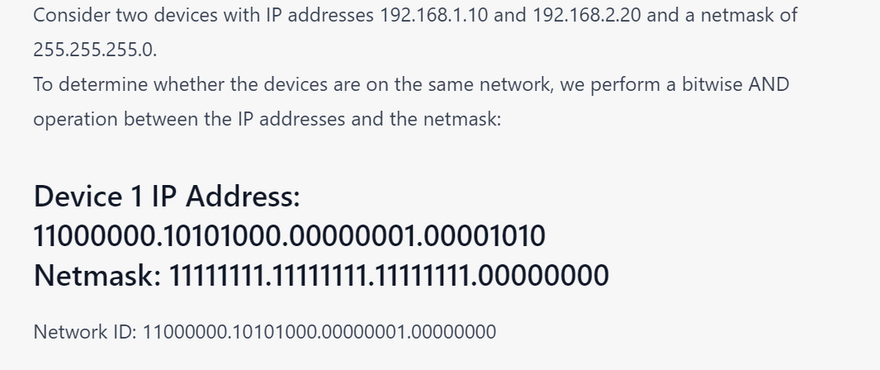
how netmask is used within same network and different network
what do u mean by RX and TX packet in ifconfig with example
what do u mean by UP,BROADCAST,LOOPBACK,RUNNING,MULTICAST with step by step example
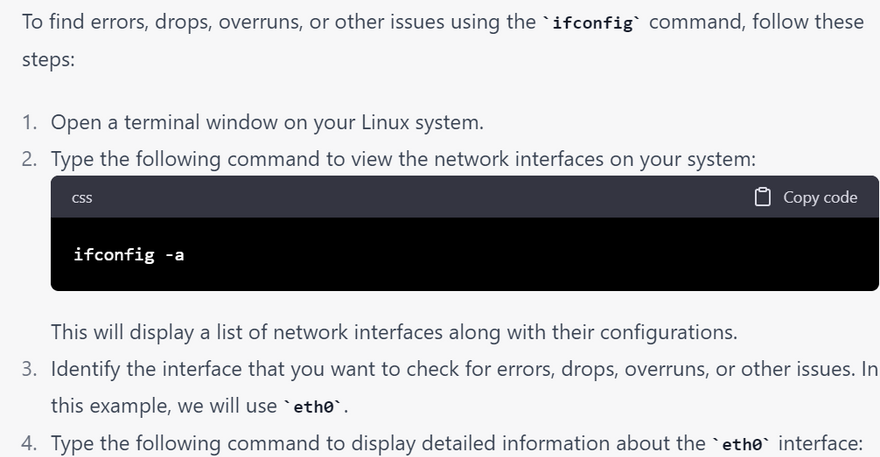
ifconfig is a command-line tool used in Unix-like operating systems to configure and manage network interfaces. While it is primarily used to view and change network interface configurations, it can also be used for troubleshooting network issues. Some ways ifconfig can be used for troubleshooting networks are:
Checking interface status: ifconfig can be used to check the status of a network interface, such as whether it is up or down, whether it has an IP address assigned, and whether it has received any packets. This information can help troubleshoot issues related to connectivity or network configuration.
Configuring IP addresses: ifconfig can be used to assign or change IP addresses and netmasks on network interfaces. This can be useful in diagnosing network configuration issues, such as if a device is unable to communicate with other devices on the network.
Enabling or disabling interfaces: ifconfig can also be used to enable or disable network interfaces. This can be useful in troubleshooting issues related to specific interfaces, such as if a network interface is malfunctioning or causing issues with the network.
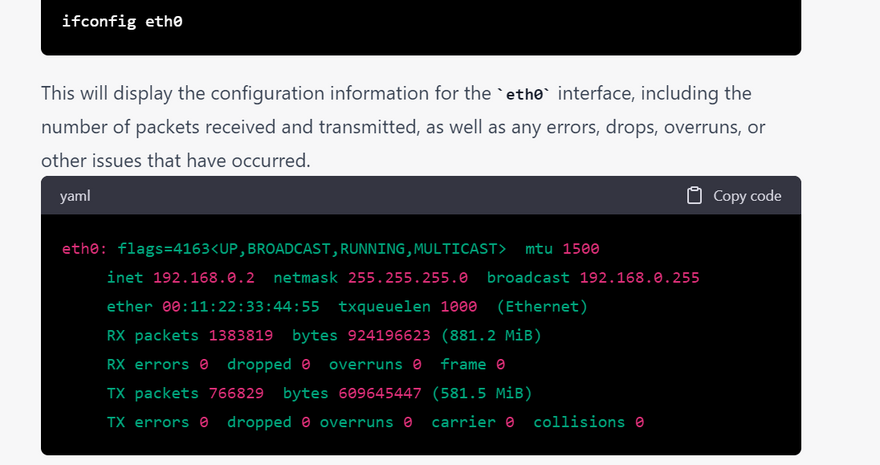
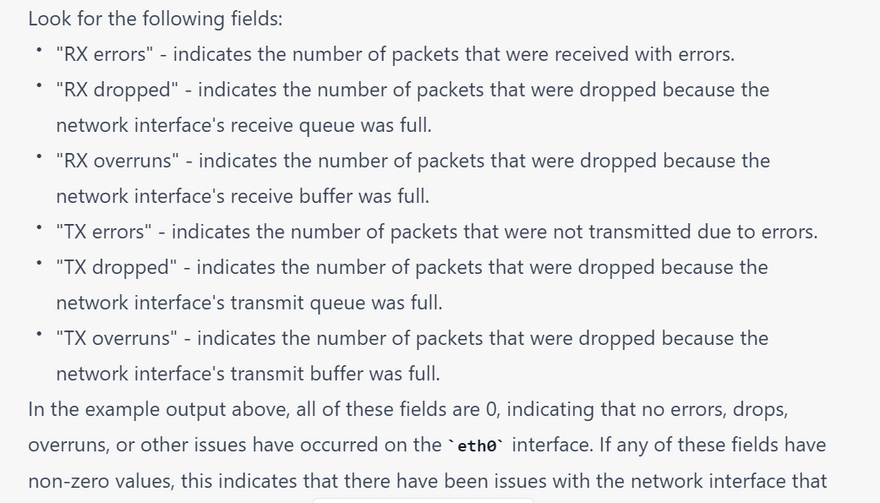
Viewing interface statistics: ifconfig can be used to view various statistics related to a network interface, such as the number of packets sent and received, the number of errors encountered, and the amount of data transmitted. This information can help diagnose network performance issues or identify potential bottlenecks.
Overall, ifconfig can be a valuable tool for troubleshooting network issues, but it is important to note that its functionality may vary depending on the operating system and version being used. Additionally, some of the tasks described above may require elevated privileges or administrator access to perform.
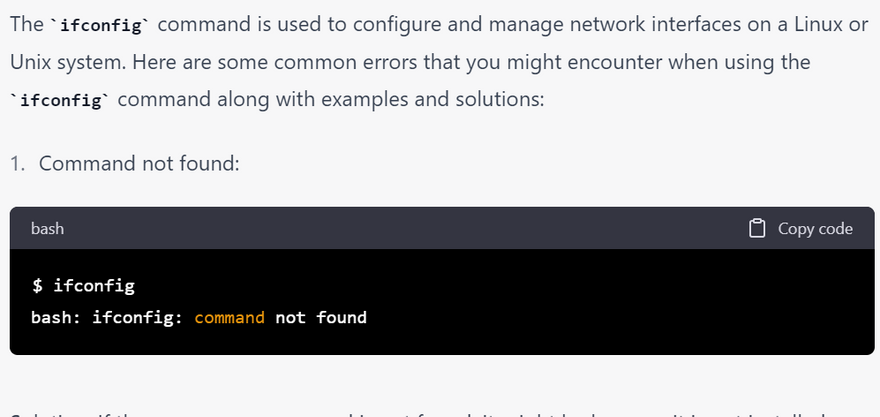
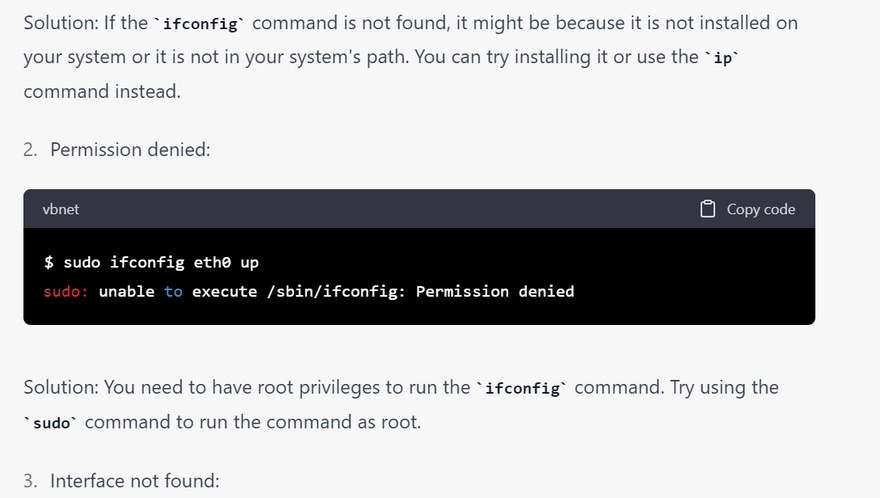
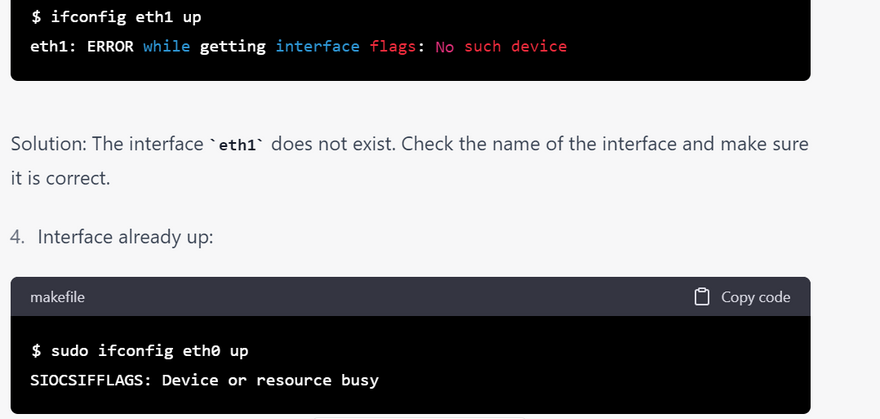
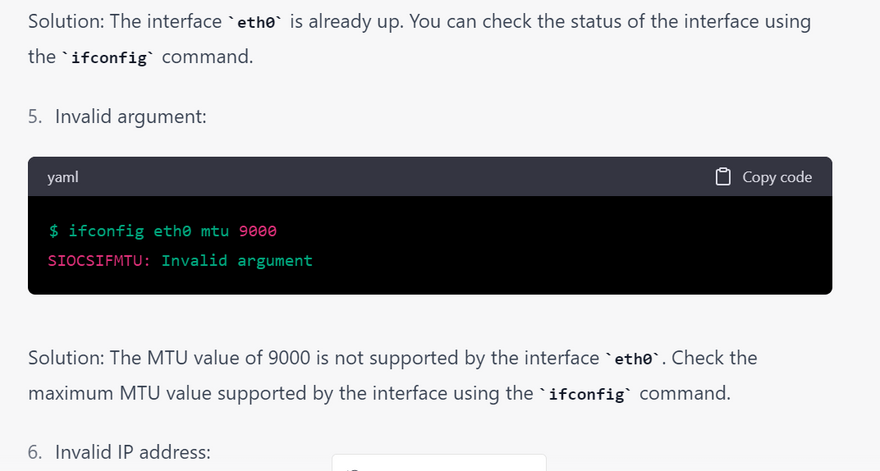
checklist of error for ifconfig commands with examples
checklist of error for ifconfig commands with examples
why broadcast address is used with example
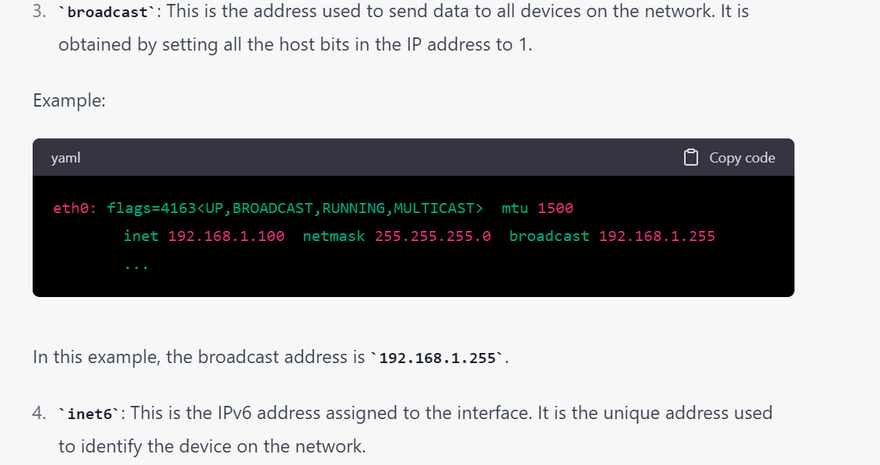
A broadcast address is used to send a message to all devices on a particular network or subnet. When a device sends a message to a broadcast address, the message is delivered to all devices on that network or subnet, allowing the sender to communicate with multiple devices simultaneously.
For example, let's say you have a network with the IP address range 192.168.1.0/24. This means that the network has 256 IP addresses, ranging from 192.168.1.0 to 192.168.1.255. The subnet mask for this network is 255.255.255.0.
The broadcast address for this network is 192.168.1.255. If you send a message to this address, it will be delivered to all devices on the network, allowing you to communicate with multiple devices at once.
Here's an example of how this might be used: let's say you want to send a message to all devices on your network to let them know that the network will be down for maintenance. You could send a broadcast message to the IP address 192.168.1.255, and all devices on the network would receive the message, allowing them to prepare for the network outage.
why netmask is used with example
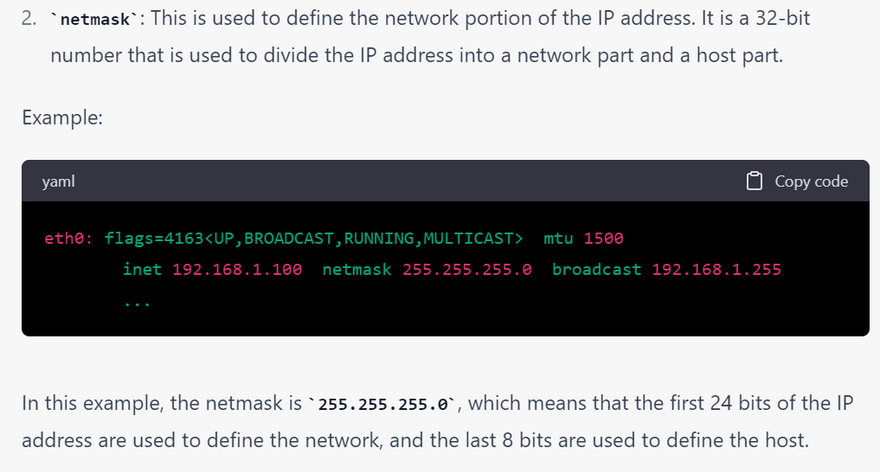
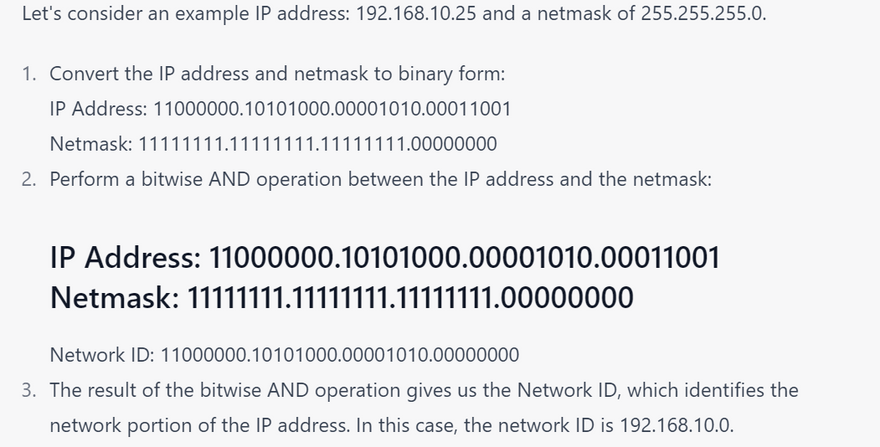
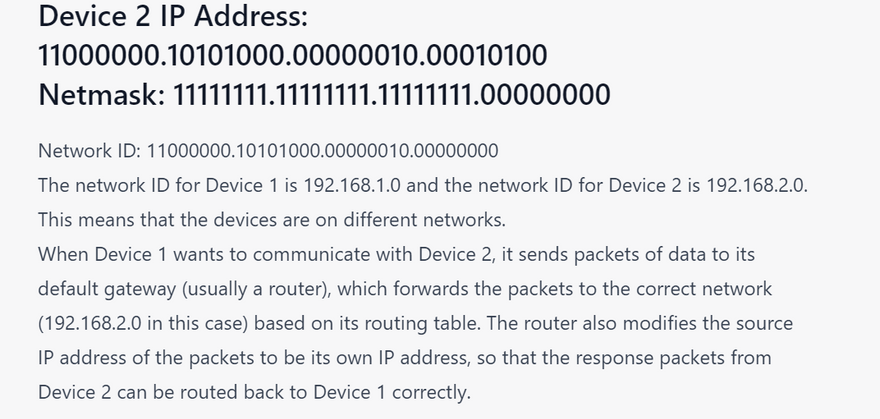
A netmask is used to identify the network portion and the host portion of an IP address. It is a binary mask that is used to divide an IP address into two parts: the network address and the host address. The netmask determines which portion of the IP address belongs to the network and which portion belongs to the host.
For example, consider the IP address 192.168.1.100 with a netmask of 255.255.255.0. The netmask specifies that the first three octets of the IP address (192.168.1) represent the network portion, and the last octet (100) represents the host portion. This means that any device with an IP address that starts with 192.168.1 is on the same network, and any device with a different network portion is on a different network.
The netmask is used in networking to determine how to route packets of data between networks. When a device wants to send data to another device on a different network, it uses the netmask to determine whether the destination device is on the same network or a different network. If the destination device is on a different network, the sending device forwards the data to its default gateway, which is responsible for forwarding the data to the correct network.
In summary, the netmask is used to identify the network portion and the host portion of an IP address, and it is used in networking to route packets of data between networks.

Top comments (0)