Reference1
Reference2
Reference3
Reference4
Reference5
Reference6
Reference7
Reference7
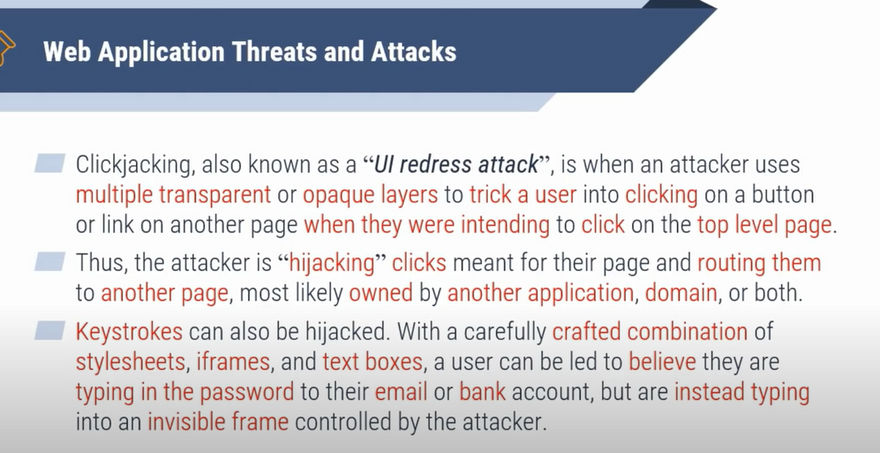
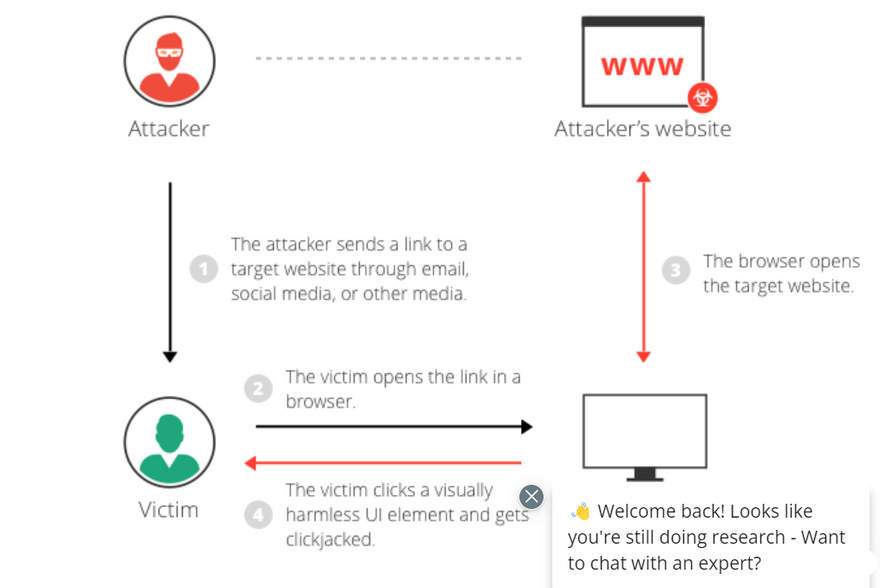
What is Clickjacking
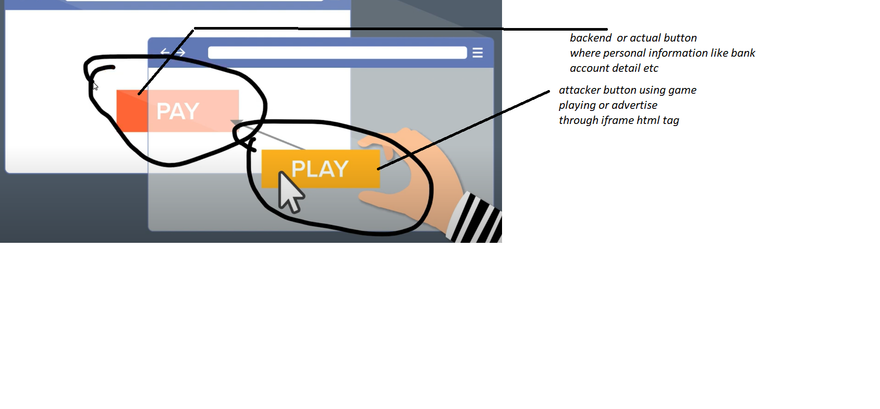
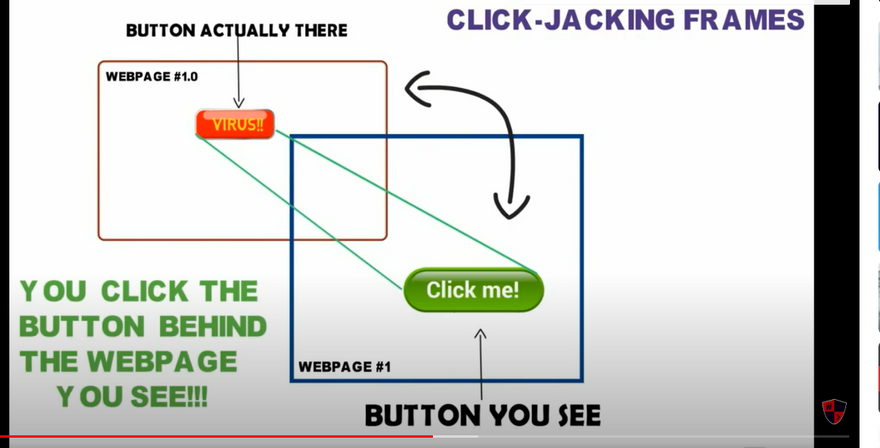
Clickjacking is an attack that tricks a user into clicking a webpage element which is invisible or disguised as another element. This can cause users to unwittingly download malware, visit malicious web pages, provide credentials or sensitive information, transfer money, or purchase products online.
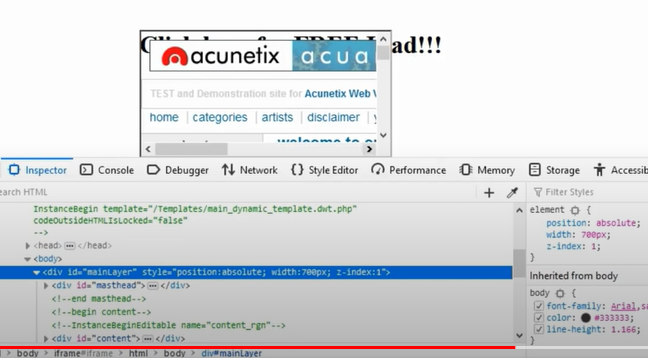
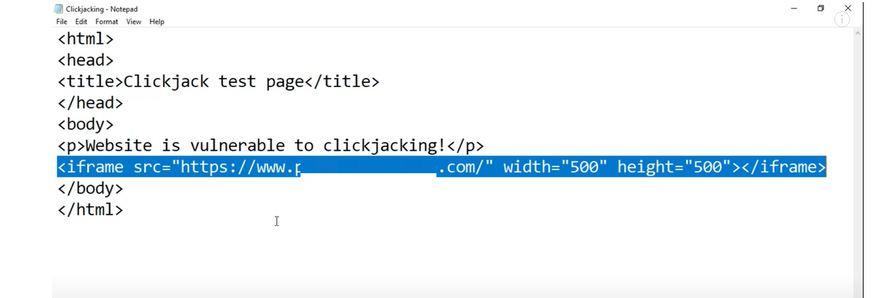
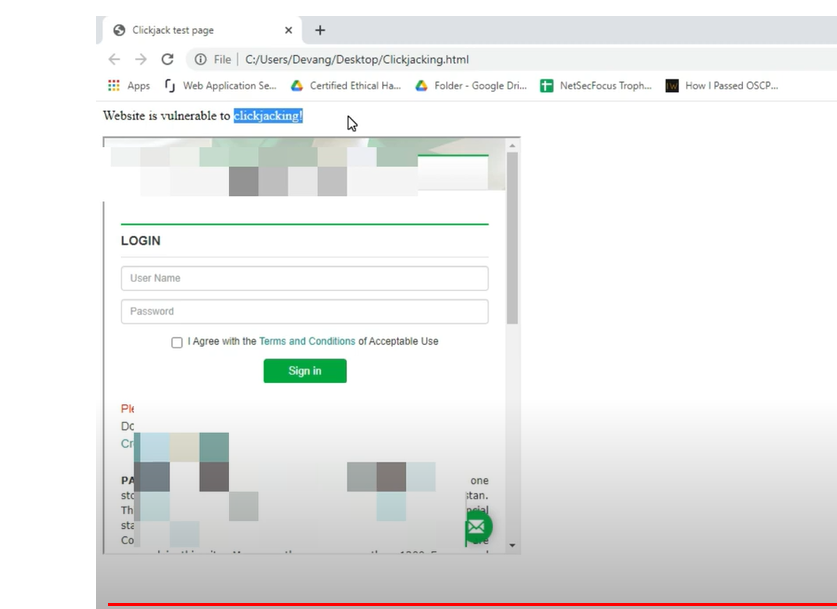
Typically, clickjacking is performed by displaying an invisible page or HTML element, inside an iframe, on top of the page the user sees. The user believes they are clicking the visible page but in fact they are clicking an invisible element in the additional page transposed on top of it.
The invisible page could be a malicious page, or a legitimate page the user did not intend to visit – for example, a page on the user’s banking site that authorizes the transfer of money.
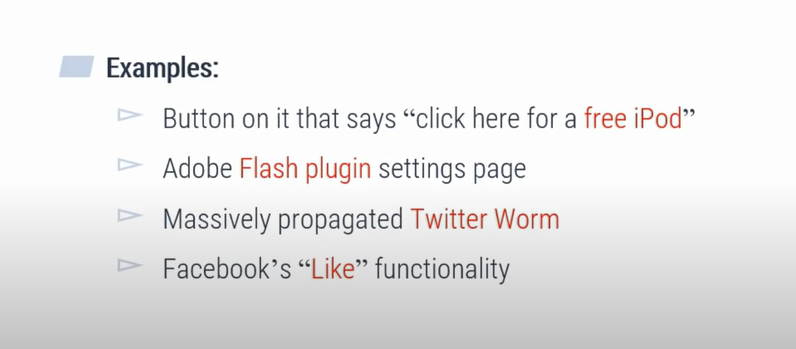
There are several variations of the clickjacking attack, such as:
Likejacking – a technique in which the Facebook “Like” button is manipulated, causing users to “like” a page they actually did not intend to like.
Cursorjacking – a UI redressing technique that changes the cursor for the position the user perceives to another position. Cursorjacking relies on vulnerabilities in Flash and the Firefox browser, which have now been fixed.
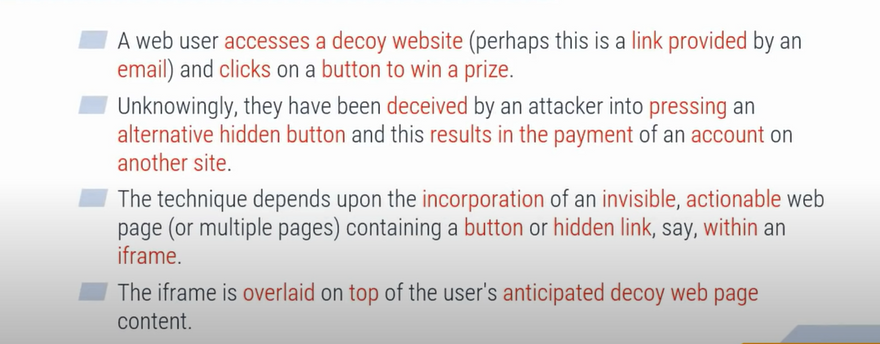
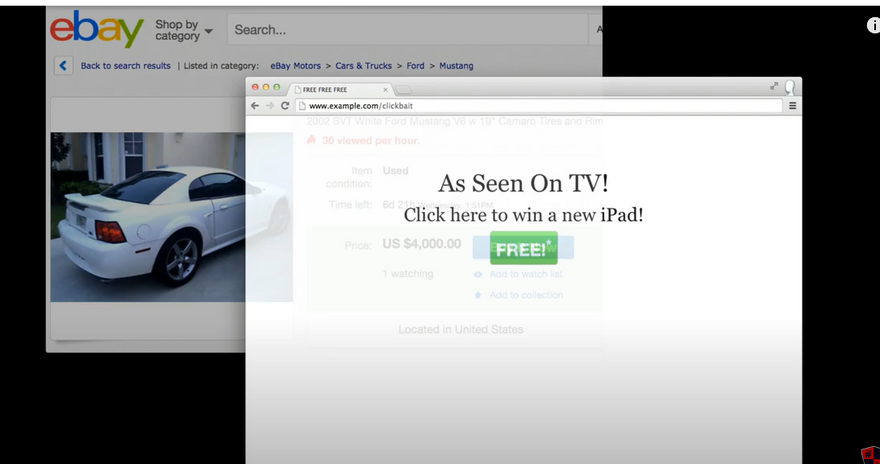
Clickjacking attack example
==========OR================
- The attacker creates an attractive page which promises to give the user a free trip to Tahiti.
- In the background the attacker checks if the user is logged into his banking site and if so, loads the screen that enables transfer of funds, using query parameters to insert the attacker’s bank details into the form.
- The bank transfer page is displayed in an invisible iframe above the free gift page, with the “Confirm Transfer” button exactly aligned over the “Receive Gift” button visible to the user.
- The user visits the page and clicks the “Book My Free Trip” button.
- In reality the user is clicking on the invisible iframe, and has clicked the “Confirm Transfer” button. Funds are transferred to the attacker.
- The user is redirected to a page with information about the free gift (not knowing what happened in the background).
This example illustrates that, in a clickjacking attack, the malicious action (on the bank website, in this case) cannot be traced back to the attacker because the user performed it while being legitimately signed into their own account.
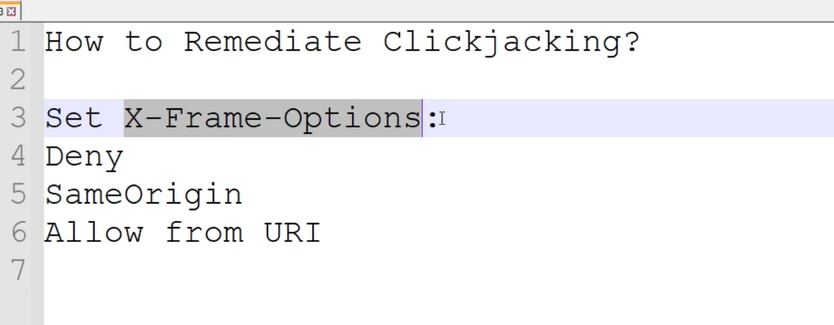
Clickjacking mitigation
There are two general ways to defend against clickjacking:
Client-side methods – the most common is called Frame Busting. Client-side methods can be effective in some cases, but are considered not to be a best practice, because they can be easily bypassed.
Server-side methods – the most common is X-Frame-Options. Server-side methods are recommended by security experts as an effective way to defend against clickjacking.
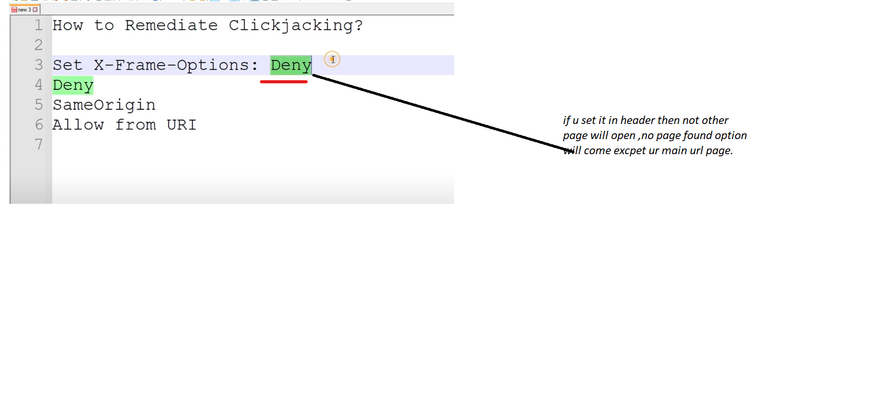
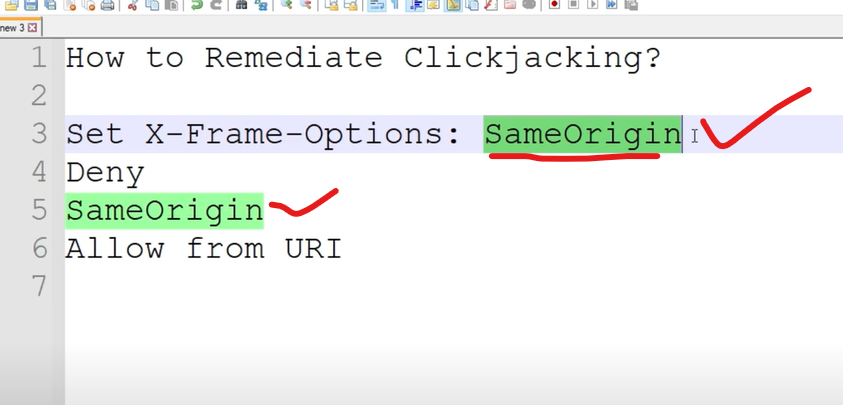
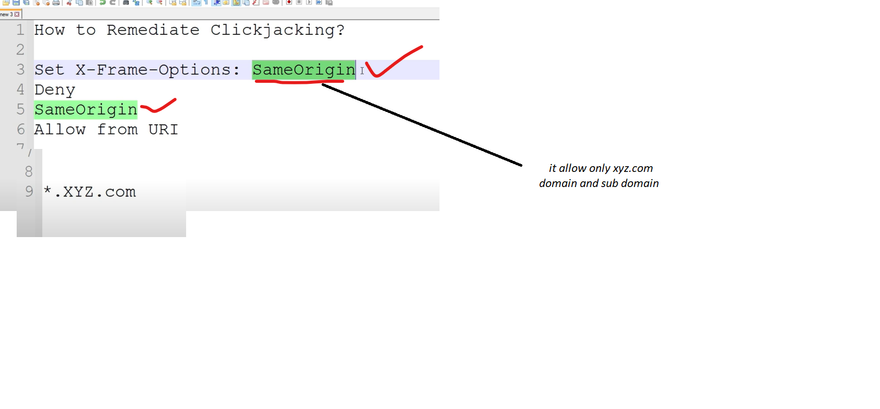
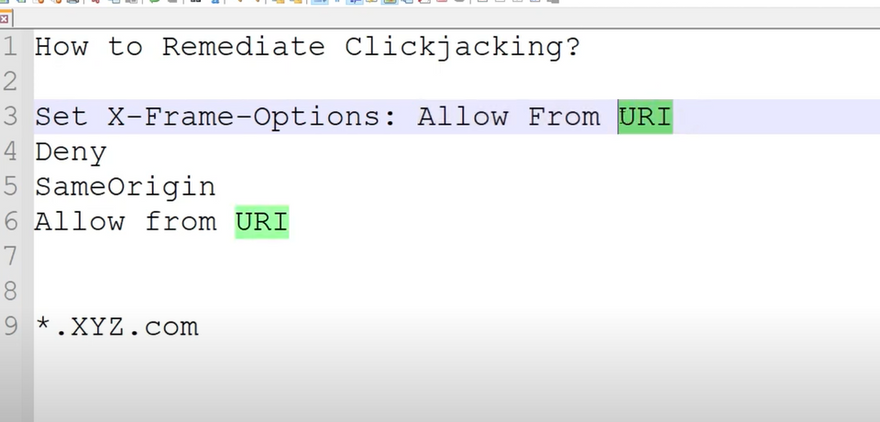
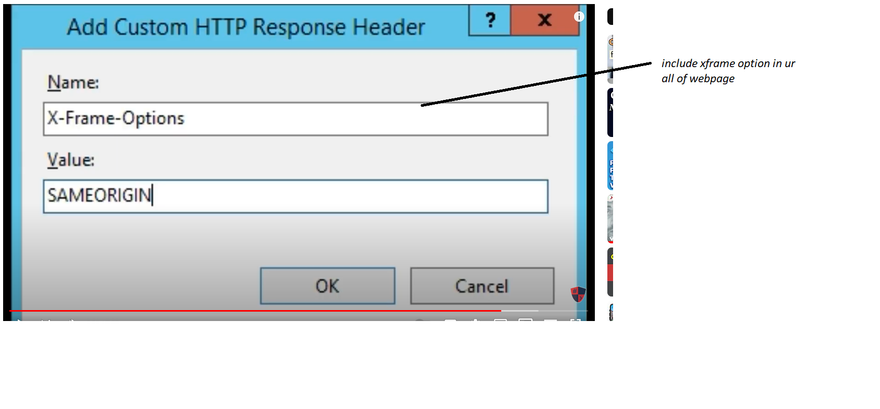
Mitigating clickjacking with X-Frame-Options response header
The X-Frame-Options response header is passed as part of the HTTP response of a web page, indicating whether or not a browser should be allowed to render a page inside a or tag.
There are three values allowed for the X-Frame-Options header:
DENY – does not allow any domain to display this page within a frame
SAMEORIGIN – allows the current page to be displayed in a frame on another page, but only within the current domain
ALLOW-FROM URI – allows the current page to be displayed in a frame, but only in a specific URI – for example www.example.com/frame-page
Another Solution
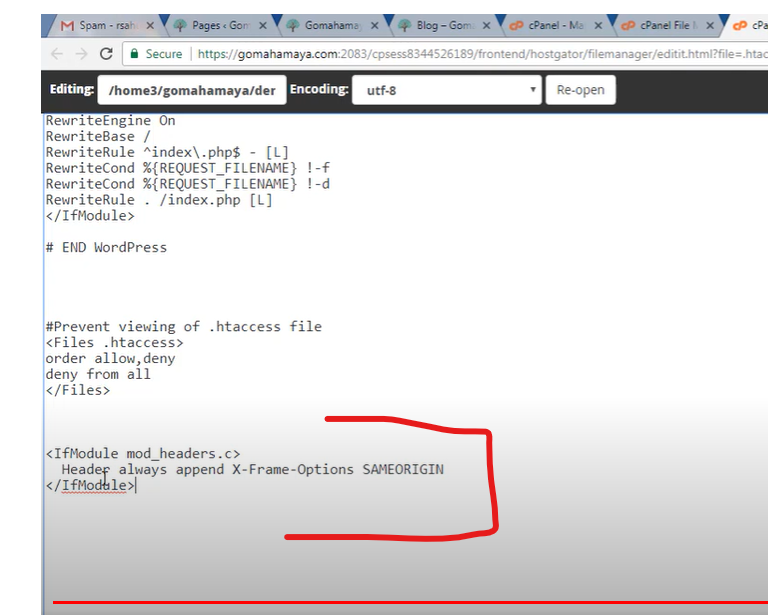
include xframe option in every webpage after click
include captcha option in every webpage after click
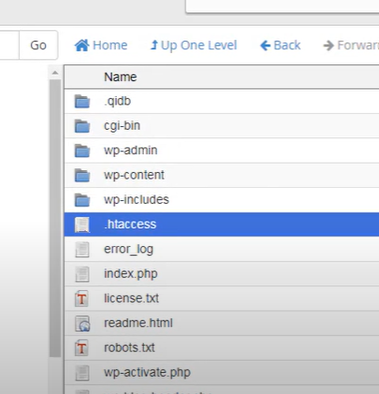
Protect clickjacking using .htacess

Top comments (0)