How to check if port is in use in
How to Check If a Port Is in Use in Linux
Ways to Find Out List of All Open Ports in Linux
QUESTION
How to Check If a Port Is in Use in Linux
How to Check If a Port Is in Use in Linux
linux-check-if-port-is-in-use-command
linux-check-if-port-is-in-use-command
ways-to-find-out-list-of-all-open-ports-in-linux
ways-to-find-out-list-of-all-open-ports-in-linux
Finding the PID of the Process Using a Specific Port
find-process-using-port
How to Check If a Port Is in Use in Linux
o check the listening ports and applications on Linux:
Open a terminal application i.e. shell prompt.
Run any one of the following command on Linux to see open ports:
sudo lsof -i -P -n | grep LISTEN
sudo netstat -tulpn | grep LISTEN
sudo ss -tulpn | grep LISTEN
sudo lsof -i:22 ## see a specific port such as 22 ##
sudo nmap -sTU -O IP-address-Here
For the latest version of Linux use the ss command. For example, ss -tulw
Let us see commands and its output in details.
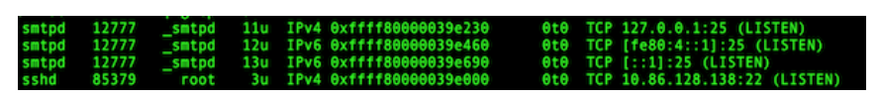
Option #1: lsof command
The syntax is:
sudo lsof -i -P -n
sudo lsof -i -P -n | grep LISTEN
doas lsof -i -P -n | grep LISTEN # OpenBSD #
Consider the last line from above outputs:
sshd 85379 root 3u IPv4 0xffff80000039e000 0t0 TCP 10
sshd is the name of the application.
- 10.86.128.138 is the IP address to which sshd application bind to (LISTEN)
- 22 is the TCP port that is being used (LISTEN)
- 85379 is the process ID of the sshd process
Viewing the Internet network services list
The /etc/services is a text file mapping between human-friendly textual names for internet services and their underlying assigned port numbers and protocol types. Use the cat command or more command/less command to view it:
less /etc/services
A sample file:
tcpmux 1/tcp # TCP port service multiplexer
echo 7/tcp
echo 7/udp
discard 9/tcp sink null
discard 9/udp sink null
systat 11/tcp users
daytime 13/tcp
daytime 13/udp
netstat 15/tcp
qotd 17/tcp quote
chargen 19/tcp ttytst source
chargen 19/udp ttytst source
ftp-data 20/tcp
ftp 21/tcp
fsp 21/udp fspd
ssh 22/tcp # SSH Remote Login Protocol
telnet 23/tcp
smtp 25/tcp mail
time 37/tcp timserver
time 37/udp timserver
whois 43/tcp nicname
tacacs 49/tcp # Login Host Protocol (TACACS)
tacacs 49/udp
domain 53/tcp # Domain Name Server
domain 53/udp
Each line describes one service, and is of the form:
service-name port/protocol [aliases ...]
ssh 22/tcp # SSH Remote Login Protocol
time 37/tcp timserver
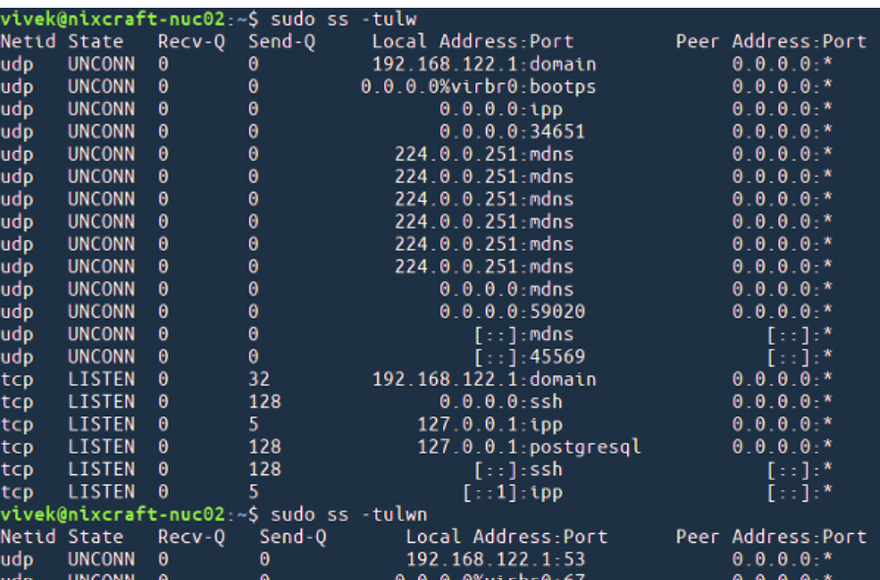
Option #2: netstat or ss command
You can check the listening ports and applications with netstat as follows.
Linux netstat syntax
Run netstat command along with grep command to filter out port in LISTEN state:
netstat -tulpn | grep LISTEN
The netstat command deprecated for some time on Linux. Therefore, you need to use the ss command as follows:
sudo ss -tulw
sudo ss -tulwn
sudo ss -tulwn | grep LISTEN
Where, ss command options are as follows:
-t : Show only TCP sockets on Linux
-u : Display only UDP sockets on Linux
-l : Show listening sockets. For example, TCP port 22 is opened by SSHD server.
-p : List process name that opened sockets
-n : Don’t resolve service names i.e. don’t use DNS
FreeBSD/macOS (OS X) netstat syntax
The syntax is as follows:
netstat -anp tcp | grep LISTEN
netstat -anp udp | grep LISTEN
OpenBSD netstat syntax
netstat -na -f inet | grep LISTEN
netstat -nat | grep LISTEN
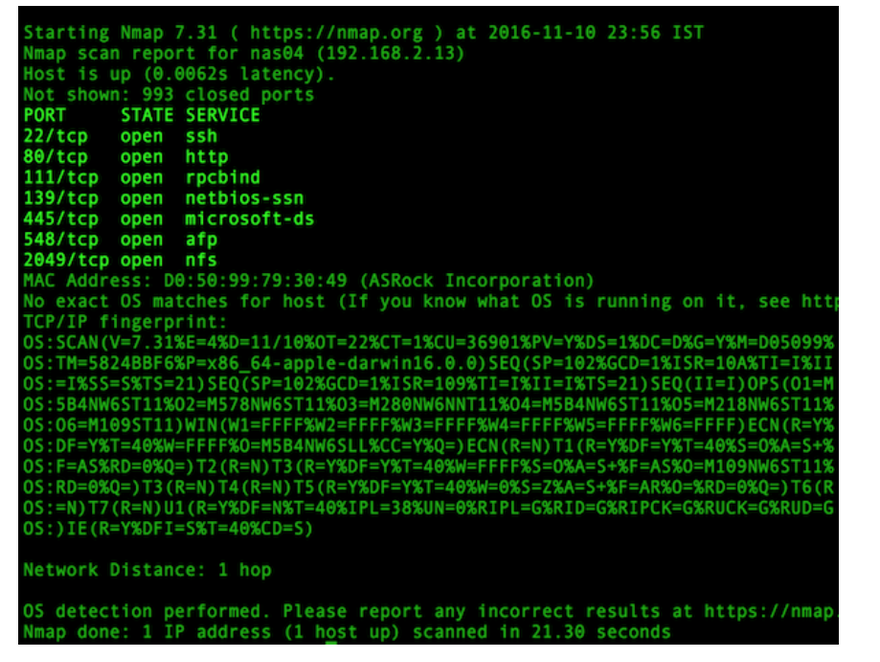
Option #3: nmap command
The syntax is:
sudo nmap -sT -O localhost
sudo nmap -sU -O 192.168.2.13 ##[ list open UDP ports ]##
sudo nmap -sT -O 192.168.2.13 ##[ list open TCP ports ]##
You can combine TCP/UDP scan in a single command:
sudo nmap -sTU -O 192.168.2.13
A note about Windows users
You can check port usage from Windows operating system using following command:
netstat -bano | more
netstat -bano | grep LISTENING
netstat -bano | findstr /R /C:"[LISTEING]"
This page explained command to determining if a port is in use on Linux or Unix-like server. For more information see the nmap command and lsof command page online here or by typing the man command as follows:
man lsof
man ss
man netstat
man nmap
man 5 services
How to Check If a Port Is in Use in Linux
If you are from a computer science background or even a little bit familiar with networking, then you may have heard of the TCP/IP stack. The TCP/IC stack comprises of five different layers, namely, the Physical Layer, Data Link Layer, Network Layer, Transport Layer, and Application Layer. Every layer of the TCP/IP stack has a different means of communication, and all communication within the Transport Layer is done via port numbers.
A port number is used to uniquely identify a device alongside the IP address. Inter-process communication is common when using computer systems. To facilitate this communication, operating systems keep certain ports open, depending upon the entity with which the user wishes to communicate. So, at any single instance, multiple ports can be open in your system.
When we say that a port is in use, we are essentially referring to a port that is open, or, in other words, a port that is in the listening state (ready to accept connections). There are multiple ways of determining the ports that are open in an operating system. This article shows you four possible methods to use to check whether a port is in use in Linux.
To determine whether a port is in use in Linux Mint 20, any of the following four methods can be used.
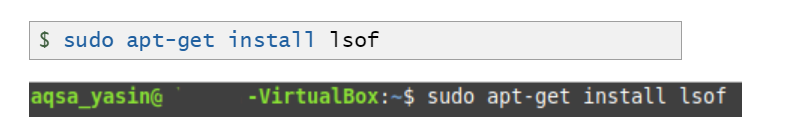
Method 1: Using the lsof Command
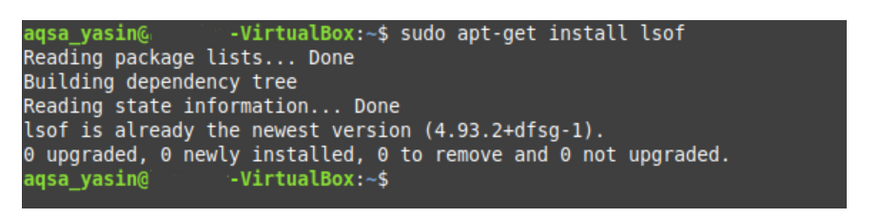
The lsof command can be used to list all the ports in use in your system in the following manner:
Upon the successful installation of the command, you will see the following output in the terminal:
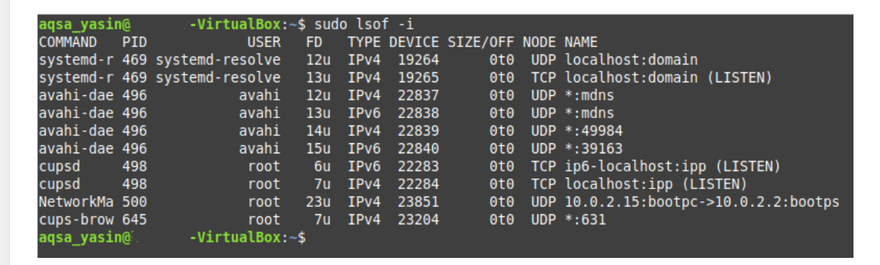
Once this command has been installed, it can be used for querying any ports that are in use in Linux. To check your system for open ports, execute the following command in your terminal:
$ sudo lsof –i
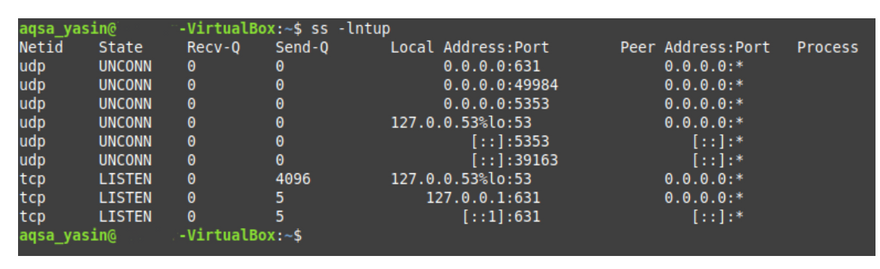
Method 2: Using the ss Command
The ss command can be used to determine any open TCP and UDP ports in your system in the following manner:
To query both the TCP and UDP ports that are in use, execute the following command in the terminal:
$ ss –lntup
In the output of this command, the ports (both TCP and UDP) that are in use have the “LISTEN” state, whereas all the other ports show the “UNCONN” state.
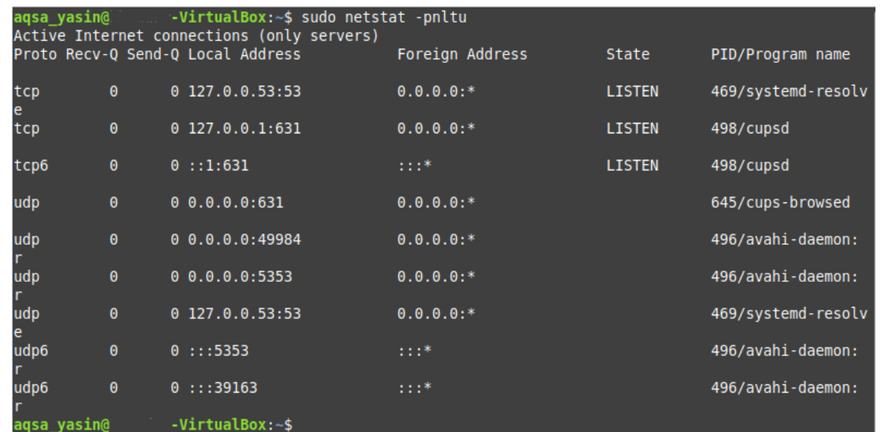
Method 3: Using the netstat Command
The netstat command can also be used to determine any open TCP and UDP ports in your system in the following manner:
To query for the TCP and UDP ports that are in use, run the following command in the terminal:
$ sudo netstat –pnltu
If you try to run this command without the “sudo” keyword, you will not be able to access all the ports. If you are logged in with the root user account, then you may skip this keyword.
When you run this command, you will be able to see that all ports in use are in the “LISTEN” state, whereas the states of all other ports are unavailable, as shown in the image below
Method 4: Using the nmap Command
The nmap command is yet another utility that can be used to determine the TCP and UDP ports that are in use in the following manner:
If the nmap utility is not yet installed on your Linux Mint 20 system, as it does not come installed by default, you may have to manually install it. To do so, execute the following command:
$ sudo apt install nmap

Top comments (0)